Teeputrseepooy: Identifier Presence Overview
Teeputrseepooy presents a structured framework for managing digital identities. This comprehensive Identifier Presence Overview addresses the complexities of privacy and data sharing in today’s digital landscape. By enhancing user understanding, it promotes informed decision-making and innovative personal data management solutions. The toolkit’s implications for autonomy and control over information are significant. However, the nuances of its application and effectiveness warrant further exploration.
Understanding the Principles of Teeputrseepooy
The principles of Teeputrseepooy encompass a framework designed to enhance understanding and application within its respective field.
At its core, these teeputrseepooy principles are grounded in foundational concepts that facilitate a deeper comprehension of complex systems.
This structured approach empowers individuals to explore and navigate intricacies, fostering an environment where freedom of thought and innovative solutions can thrive.
Key Features and Benefits of the Framework
Key features of the Teeputrseepooy framework are designed to provide a comprehensive toolkit for practitioners, enhancing both theoretical understanding and practical application.
The framework’s advantages include improved identifier efficiency, facilitating streamlined processes and decision-making.
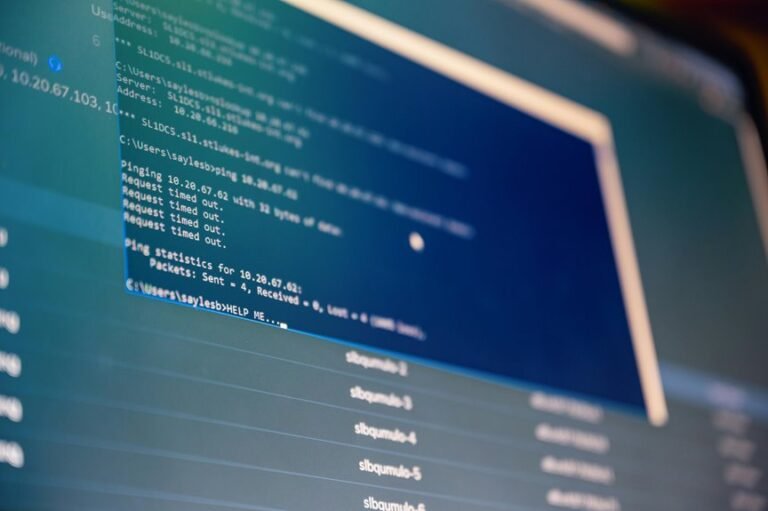
Practical Applications in the Digital Landscape
In the rapidly evolving digital landscape, the Teeputrseepooy framework demonstrates significant versatility across various applications.
It enhances digital identity management, allowing users to maintain control over their personal information. Furthermore, it bolsters online privacy by providing secure methods for data sharing and authentication.
This adaptability positions Teeputrseepooy as a vital tool for individuals seeking to navigate the complexities of digital interactions responsibly and freely.
Conclusion
In conclusion, Teeputrseepooy’s Identifier Presence Overview equips users with essential tools to navigate the complexities of digital identity management. By adopting this framework, individuals can enhance their privacy and data-sharing practices. For example, a small business owner could utilize this toolkit to streamline customer data handling, ensuring compliance with privacy regulations while fostering trust with clients. Such practical applications illustrate the framework’s capacity to empower users in maintaining control over their digital footprints in an increasingly interconnected world.